Open-Source Intelligence
Open-Source Intelligence (OSINT) is the practice of building a picture of a person, organization, or event using only information that is publicly accessible. On FaceCheck.ID, OSINT often starts with a single photo: a face match surfaces a username, a profile, or an old forum post, and the investigator works outward from there to confirm whether the person is who they claim to be.
How face search fits into an OSINT workflow
A face is one of the most reliable pivot points in an investigation because it travels across platforms even when names, handles, and bios change. Someone running a romance scam can rotate through dozens of fake names, but if they reuse the same stolen photo, reverse face search can connect those identities. The same logic applies to recruiters checking a candidate, journalists verifying a source, or fraud teams reviewing suspicious accounts.
A typical face-led OSINT process looks like this:
- Start with a known image, such as a dating profile photo or a LinkedIn headshot.
- Run a face search to find other pages where that face appears.
- Pull usernames, real names, and bio details from each match.
- Pivot into traditional OSINT: search engines, public records, breach data, image metadata, and archived pages.
- Cross-check timestamps, locations, and writing style to confirm or rule out a single identity.
The face match is rarely the conclusion. It is the lead that points you toward sources you can verify through other means.
What public data tells you, and what it does not
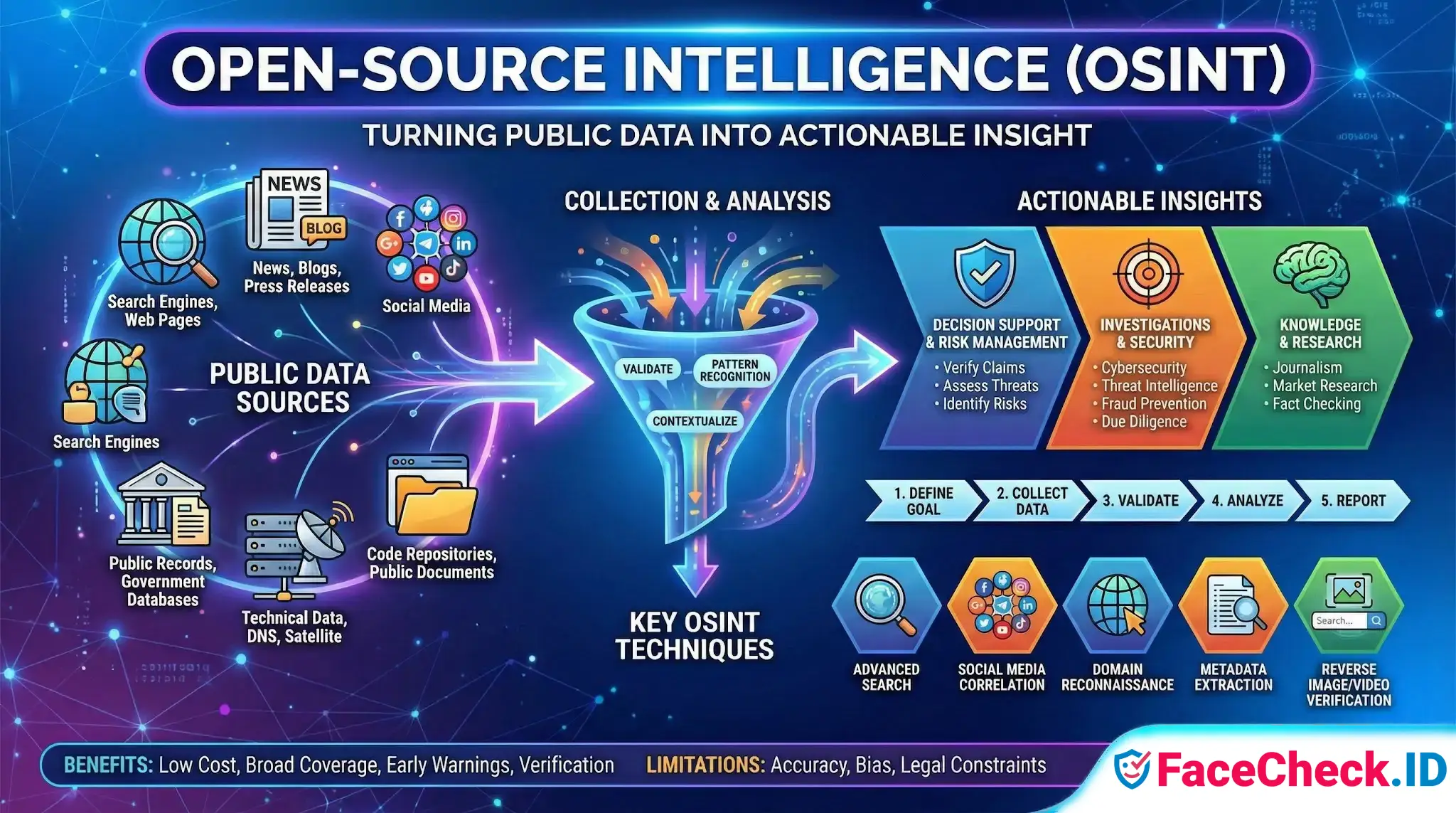
OSINT relies on information anyone can legally access: indexed web pages, social profiles set to public, news articles, court records, company filings, and images crawled by search engines. Face search engines work the same way. They index faces from publicly reachable pages and return links back to those pages. They do not access private accounts, locked profiles, or anything behind authentication.
This matters for interpretation. A face match on a public Instagram post is meaningful because the post was shared publicly. A lack of matches is not proof someone has no online presence, only that no indexed public page contains a recognizable version of that face. Strict privacy settings, recent uploads, group photos with cropped faces, and low-resolution images all reduce what an OSINT investigator can find.
Common OSINT scenarios where face search is decisive
- Catfishing checks: A profile claims to be a 32-year-old engineer in Denver, but the face matches a Brazilian fitness model whose photos have been reused across scam sites for years.
- Vendor and executive due diligence: A consultant's headshot appears on a stock photo site rather than on any verifiable employer page.
- Missing person leads: Family members search using older photos, then use OSINT to follow up on any matching social profiles or news mentions.
- Sextortion and harassment investigations: Victims trace anonymous accounts back to real identities by matching the operator's profile photo to a public account they forgot to clean up.
- Journalism: Reporters confirm whether a quoted "expert" exists, or trace propaganda accounts back to their real owners.
In each case the face is the pivot, and the rest of the OSINT toolkit, such as username correlation, archived pages, breach lookups, image metadata, and reverse search of background details in the photo, does the confirmation work.
Limits, false leads, and ethical lines
Face search produces probabilistic matches, not identifications. Two people can look strikingly similar, especially at low confidence scores, and a high score on a single low-quality image is not the same as a confirmed identity. Lookalikes, twins, heavily edited images, and AI-generated faces all create false positives. Old photos can also mislead, since a face from ten years ago may match a current profile that belongs to a different person reusing the image.
Good OSINT practice treats a face match as a lead requiring corroboration through independent public sources. It also respects legal and ethical limits: do not bypass access controls, do not harass subjects, do not publish personal data without cause, and remember that a public photo does not give you full context about the person in it. Face search is powerful precisely because it cuts through identity manipulation, which is the same reason it has to be used carefully.
FAQ
What does “Open-Source Intelligence (OSINT)” mean when using face recognition search engines?
Open-Source Intelligence (OSINT) is the practice of collecting and analyzing information from publicly available sources. In the context of face recognition search engines, OSINT typically means using face-match results as leads to discover where a face image appears online (e.g., public webpages, reposts, news pages, forums), then validating those leads with additional open-source checks rather than treating a match as proof of identity.
What are common OSINT workflows after you get results from a face recognition search engine?
Common OSINT workflows include: (1) open the result URLs and confirm the face context (same person vs look-alike), (2) trace the earliest/most authoritative source (original upload vs reposts/screenshots), (3) corroborate with non-face indicators such as consistent usernames, timestamps, locations, and cross-links, (4) run parallel checks (reverse image search for duplicates, keyword searches for handles), and (5) document findings with links and dates while keeping conclusions tentative unless independently verified.
How do OSINT analysts reduce misidentification risk when using face recognition search engines?
They treat face matches as hypotheses, not identifications; verify with multiple independent sources; look for consistency across time (age progression, recurring context); compare multiple photos of the same subject rather than relying on a single image; be cautious with low-quality, filtered, or AI-generated images; and avoid making high-stakes claims (accusations, doxxing, reporting) unless there is strong corroboration beyond the face similarity.
What kinds of open sources can bias or distort OSINT conclusions from face-search results?
Open sources can be misleading due to repost networks, meme pages, aggregators, scraped “public record” and mugshot-style sites, fan pages, and mislabeled uploads. These sources can create false associations (e.g., attaching a face to the wrong name or story), so OSINT practice emphasizes checking primary/earliest sources, evaluating credibility, and confirming context rather than trusting the first matching page.
How can FaceCheck.ID add value in an OSINT workflow for face recognition search engines?
In an OSINT workflow, FaceCheck.ID can be used as one lead-generation step to locate webpages where a similar face appears. The value is in widening discovery (finding candidate pages to review) and enabling cross-checking against other tools and open-source indicators. As with any face search engine, results should be validated by reviewing the linked pages and corroborating with additional OSINT evidence before drawing conclusions about identity.

Recommended Posts Related to open-source-intelligence
-
Leveraging Facial Recognition Technology to Combat Human Trafficking
The Impact of Open-Source Intelligence (OSINT) on Human Trafficking Cases. Combining facial recognition with open-source intelligence (OSINT) significantly enhances the efficiency of investigations. Open-Source Intelligence (OSINT) Analysis.