Identity Theft: Image-Based Misuse
Identity theft now reaches beyond stolen card numbers and tax returns. Faces have become a form of credential, and stolen photos let criminals build convincing personas, open accounts, and pass casual identity checks. Reverse face search is one of the few tools that lets a victim, or someone vetting a stranger online, find out where their face is being used without permission.
How face theft fits into modern identity theft
Most identity theft guides still focus on Social Security numbers, bank logins, and breached databases. Those threats are real, but image-based identity misuse has grown alongside them. A single high-quality headshot pulled from LinkedIn, Instagram, or a wedding photographer's portfolio can be reused to:
- Build fake dating profiles on Tinder, Hinge, Bumble, or regional apps
- Populate fraudulent escrow, crypto, or investment sites with "team" photos
- Pass low-effort KYC checks that compare a selfie to an ID photo
- Run romance scams and pig butchering schemes targeting victims worldwide
- Open social accounts used to harass, defame, or impersonate the real person
Face-search engines work on the opposite premise of traditional fraud monitoring. Instead of watching for misuse of your numbers, they scan indexed pages across the public web and surface places your face appears, including profiles you never created.
Signs your face has been pulled into someone else's identity
People often discover image-based identity theft only after a stranger contacts them, asking why they were on a dating site or why an "investment advisor" had their picture. A reverse face search tightens that feedback loop. When reviewing results, the patterns that suggest active misuse include:
- A profile using your photo with a different name, age, or country
- The same headshot reused across dating, escort, or crypto sites
- News or scam-warning blogs that posted your image as a known fraudster's avatar
- Accounts on platforms you have never used, especially ones registered in languages you do not speak
- Slightly edited versions of your photo, such as flipped, recolored, or face-swapped variants
A match alone does not prove fraud. Lookalikes exist, and false positives happen at lower confidence scores. Strong evidence usually comes from finding the same exact photo, not just a similar face, attached to an identity that is clearly not yours.
What to do after discovering image-based misuse
If a face search surfaces accounts impersonating you, the cleanup looks different from credit-card fraud. There is no central bureau to call. The work is platform by platform:
- Save URLs, screenshots, and timestamps of every impersonating profile before it disappears.
- File impersonation reports with each platform, attaching a photo ID if the platform requires it.
- Search for the same images on Google Images and other reverse-image tools to find copies the face engine missed.
- Warn anyone in your network who might be contacted by the fake account, especially on dating apps where scammers cite "mutual friends."
- Tighten what is publicly indexable: lock down social profiles, remove old portfolio pages, and request takedowns from sites that scraped your photos.
For ongoing exposure, periodic re-searches matter more than a one-time check. Scammers often rotate through stolen photo sets, dropping accounts and creating new ones every few weeks.
What face search can and cannot prove
Reverse face search shows where an image appears in the indexed public web. It does not prove who created the account, who uploaded the photo, or whether the operator is the same person across multiple profiles. Two scammers might share a stolen photo set, and one impersonator might run dozens of accounts with different faces. Results are leads, not legal evidence.
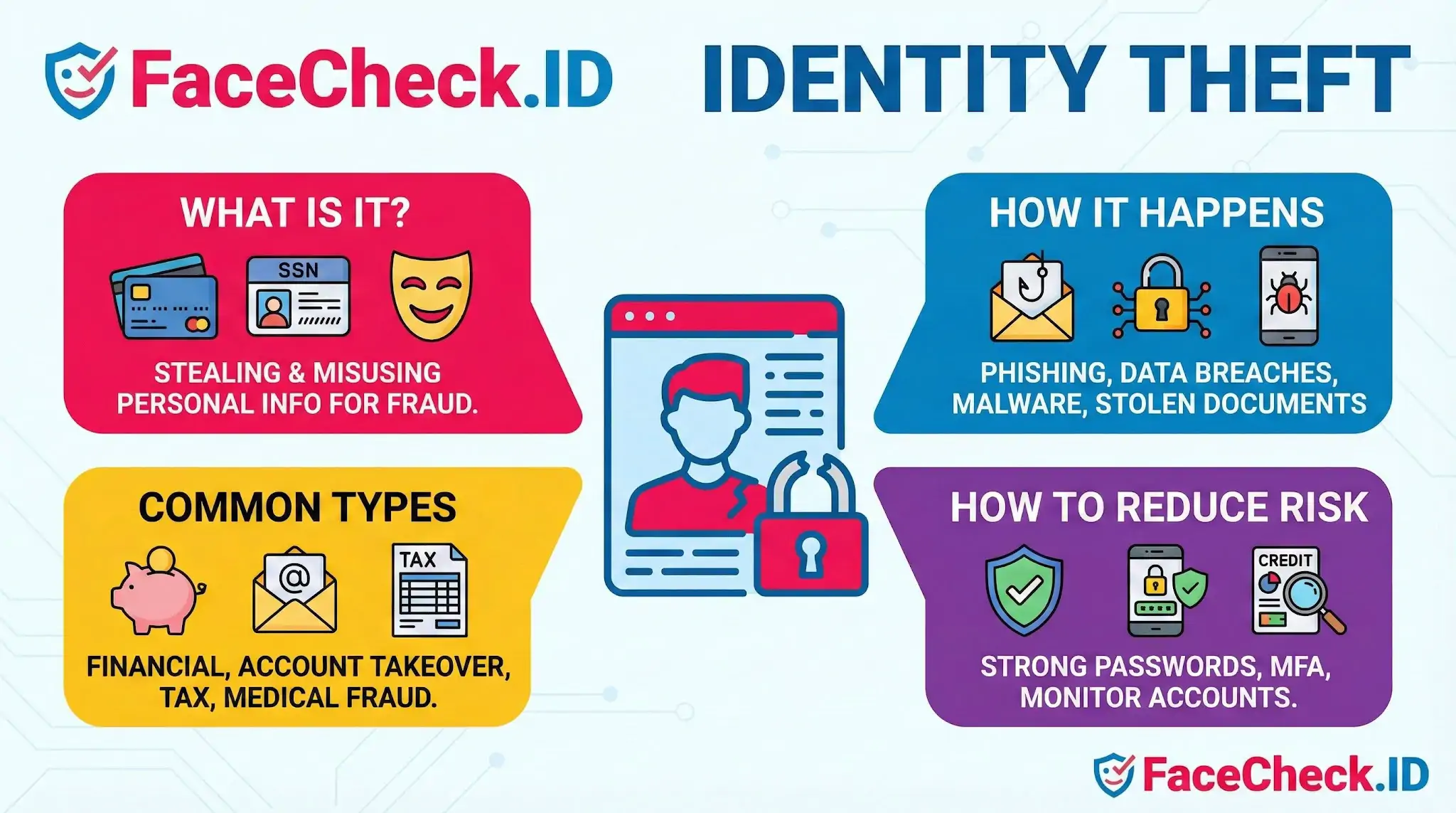
Face search also cannot recover stolen money, fix a damaged credit file, or remove content from sites that ignore takedown requests. It works alongside traditional identity-theft defenses, including credit freezes, multi-factor authentication, breach monitoring, and careful handling of personal documents. The face is one more piece of identity that can be stolen, and treating it that way is the first step in protecting it.
FAQ
How can face recognition search engines be used to detect identity theft or impersonation?
They can help you spot where a face photo is being reused across the public web (e.g., the same face appearing on multiple profiles or listings). That pattern can indicate impersonation, stolen photos, or synthetic profile activity. Treat results as leads: confirm by checking the source page context, timestamps, and whether the account shows consistent personal history.
What are common signs in face-search results that suggest someone stole a person’s photos for identity theft?
Common warning signs include: the same face tied to multiple unrelated names/usernames, the same headshot used across different platforms with conflicting biographies/locations, the photo showing up on scam-report or repost/scrape sites, and sudden clusters of near-identical profiles. Any single sign can be benign, but multiple inconsistencies raise risk.
If I find my face photo in face-search results on accounts I don’t control, what should I do to reduce identity-theft risk?
Collect evidence first (URLs, screenshots, dates), then report the impersonating accounts to each platform and request takedown. If available, use the search engine’s removal/opt-out process for the result pages. Strengthen your own accounts (unique passwords, MFA), monitor for new accounts or financial/credential misuse, and consider placing fraud alerts or credit monitoring if personal data is involved.
What are the biggest privacy and security risks of uploading a face photo to investigate identity theft, and how can I reduce them?
Risks include exposing a sensitive face image to a third party, potential retention of uploads, and linking the upload to your IP/device/browser identifiers. To reduce risk: use the minimum necessary image (crop to face, remove backgrounds), avoid including bystanders, use a fresh screenshot without metadata when possible, review the tool’s retention/removal policy, and consider using a separate browser profile or privacy protections while keeping your activity lawful.
How can FaceCheck.ID (or similar tools) help in an identity-theft investigation without over-identifying someone?
Tools such as FaceCheck.ID can help quickly surface public-web pages where a face appears, which can be useful for finding impersonating profiles or reused photos. To avoid over-identification: corroborate with multiple independent signals (same unique photos, consistent usernames, mutual links, long-lived accounts), prioritize original sources over reposts, and never treat a face match alone as proof of a person’s real-world identity.

Recommended Posts Related to identity-theft
-
How to Reverse Image Search Mugshots
Preventing identity theft: By verifying the identities of individuals in various online and offline contexts, FaceCheck.ID could contribute to reducing instances of identity theft and fraud.
-
How to Spot a Catfish Online in Under 60 Seconds with FaceCheck.ID
Identity Theft Resource. Consider Identity Theft Protection.
-
How to Find Someone with a Photo?
You can use Social Catfish to verify people, find identity thefts, ensure the credibility of dating ads, reconnect with relatives or friends, and find copyright violations of your photographs.

